 I Computer Ricondizionati per le aziende ed i professionisti, consentono sicuramente di risparmiare fino al 60% rispetto al prezzo di un prodotto nuovo di pari prestazioni.
I Computer Ricondizionati per le aziende ed i professionisti, consentono sicuramente di risparmiare fino al 60% rispetto al prezzo di un prodotto nuovo di pari prestazioni.
I Computer Ricondizionati con opportuni settaggi del sistema operativo ed upgrade hardware, possono eguagliare performaces di prodotti di fascia superiore senza impegnare il sistema operativo con applicativi che invece di renderlo più performante, ne rallentano il funzionamento aggiungendo inutili cicli di lavoro ai microprocessori.
I soldi hanno un valore e le nostre aziende considerano che è un’ottima occasione per poter rinnovare il parco macchine sfruttando la possibilità di avere il meglio con Computer Ricondizionati potendo risparmiare sull’acquisto e sostituzione di nuove macchine spesso non necessarie per poter ottenere prestazioni di lavoro migliori.
PRENDI CONTATTO CON NOI
La necessità di un nuovo Personal Computer, non significa aver bisogno dell’ ultimo modello appena uscito, ma significa avere l’esigenza di una macchina che possa sviluppare velocità maggiori, dare sicurezza nel suo utilizzo e nello stesso tempo consentirci di poterci ritrovare con un hardware completamente revisionato e forse upgradato nelle sue componenti di base.
I prodotti ricondizionati vengono smontati, verificati, ripuliti completamente subendo un processo che solitamente è utilizzato durante i cicli produttivi rendendo tra l’altro la macchina completamente sanificata, e se il computer desktop non è brandizzato viene sostituito il case (l’involucro del vostro pc), viene controllato l’alimentatore, viene sostituita la pasta termica sui componenti soggetti a maggior surriscaldamento e viene montato un hard disk SSD da 256 Giga che consente tranquillamente l’utilizzo della macchina anche con sistemi operativi Microsoft permettendogli di esprimere il massimo delle performaces, viene controllata la ram e se inferiore ai 2 Giga bytes vi verrà chiesto di ampliarla almeno a 4 Giga bytes (indispensabile condizione minima per massimizzare le prestazioni) anche se desiderate avere il sistema operativo Gnu/Linux Ubuntu Desktop Long Term.
Con i Computer Ricondizionati possono essere incluse le licenze dei sistemi operativi se si desidera Microsoft Windows 10 Professional, altrimenti le macchine verranno fornite con un sistema operativo Gnu/Linux Ubuntu Desktop Long Term che garantisce cinque anni di aggiornamenti sicuri e stabili da far invidia ad altri sistemi operativi blasonati.
Il sistema operativo Gnu/Linux Ubuntu LTS metterà in condizione il vostro hardware di godere di performances che consentiranno di sviluppare con schede madri non proprio di ultimissima generazione potendo inoltre avvalersi di un immenso contenitore di programmi open source liberamente installabili che daranno la possibilità di utilizzo spesso migliore se paragonati al software a pagamento.
L’utilizzo di Computer Ricondizionati è una scelta eco-sostenibile che aiuta il pianeta e viene incontro alle esigenze di tantissimi professionisti che vorrebbero poter risparmiare e nello stesso tempo poter riutilizzare computer che, se verificati ed upgradati nel modo corretto, possono ancora sviluppare velocità e sicurezza nel lavoro per molti anni a venire.
Il recupero di un computer e delle sue componenti evita che finiscano in discarica e contribuiscano ad inquinare con i materiali pericolosi in esso contenuti.
QUALI SONO I PROCESSI CHE SUBISCE UN COMPUTER CON IL RICONDIZIONAMENTO ?
Il computer che arriva presso la nostra struttura viene immediatamente visionato esteriormente e smontato completamente compreso il suo alimentatore.
La piastra madre verrà pulita con un liquido particolarmente efficace avendola preventivamente privata della cpu, delle memorie ed eventuali schede video e schede accessorie con la successiva sostituzione della batteria tampone.
La cpu viene bonificata dalla pasta termica e le ventole della macchina vengono verificate e pulite anch’esse prima con una soluzione alcolica e poi con un liquido di mantenimento per materiali plastici oltre che lubrificarne la meccanica con un’olio spray che ne consenta una rotazione ottimale senza attriti.
Le memorie vengono verificate e maggiore attenzione viene posta ad eventuali residui di ossido che può essersi formato con il tempo effettuandone una rimozione completa.
Anche l’alimentatore, per i Computer Ricondizionati, viene smontato e bonificato completamente operando anche sulla sua ventola, nello stesso modo di come sono state trattate le altre ventole.
Un componente della piastra madre che gestisce gli hard disk etc ed è il controller a cui solitamente nessuno pensa di smontarne il dissipatore termico, eliminando ogni traccia di pasta termica e provvedendo alla sua sostituzione consentendo una migliore efficienza per lo smaltimento del calore.
Dopo questo passaggio, viene rimontato tutto all’interno di un nuovo case se la macchina era assemblata o dello stesso case, che comunque ha subito un ciclo di sanificazione completa, se la macchina è brandizzata (di marca).
Viene sostituito l’hard disk con un disco SSD da 256 Giga bytes già pre-installato e pronto per i test che il computer dovrà subire e qualora abbia meno di 4 Gigabytes di memoria si provvederà ad implementarne la differenza per portarlo al minimo indispensabile osservando un incremento nelle prestazioni durante il suo utilizzo.
Al termine di tutto il lavoro su esposto, i Computer Ricondizionati verranno testatati con un ciclo di stress per averne garanzia di funzionalità dopo averne preventivamente settato il bios secondo specifiche idonee.
I NOTEBOOK ED I SERVER POSSONO ESSERE RICONDIZIONATI ?
NO, per motivi di tempo e quindi di costi che verrebbero imputati al cliente, non ricondizioniamo altre apparecchiature se non solo ed esclusivamente PC DESKTOP, quindi escludiamo il ricondizionamento di notebook (portatili) ed altre apparecchiature.
SE IL COMPUTER NON SI ACCENDE POSSIAMO RICHIEDERNE IL RICONDIZIONAMENTO ?
Quando un computer non si accende, se non lo abbiamo aperto o fatto aprire da qualche persona poco esperta, è probabile che il guasto sia da ricercare nell’alimentatore e quindi potremo probabilmente rivederlo nuovamente in funzione.
Il nostro personale utilizza braccialetti collegati a terra per poter operare all’interno dei computer impedendo all’energia elettrostatica di danneggiarne i componenti; questa precauzione non essendo utilizzata dalla maggior parte degli improvvisati tecnici che decidono di operare sulla componentistica elettronica, può danneggiarla irrimediabilmente non potendo garantire la riuscita del ricondizionamento e quindi della funzionalità stabile della macchina.
I Computer Ricondizionati devono funzionare perfettamente in uno stato di velocità e stabilità per consentire un lavoro adeguato e soddisfacente dell’utilizzatore, non stiamo parlando della solita assistenza tecnico informatica.
In questo caso, per completa trasparenza, riteniamo sia inutile richiederne il ricondizionamento per evitare un costo minimo che verrebbe comunque imputato.
OPERATE ANCHE SU TERRITORIO ITALIANO ?
CERTAMENTE SI’, la nostra azienda opera anche su territorio italiano avvalendosi di partners di provata esperienza e professionalità che potranno supportarvi rappresentandoci completamente.
QUALE E’ IL COSTO PER IL RICONDIZIONAMENTO DI UN COMPUTER ?
Il ricondizionamento di un computer implica un costo di 250 Euro e comprende una batteria tampone, un disco SSD, la verifica e la bonifica dell’hardware, un sistema operativo, già da noi, pre-configurato con installato un minimo di software per un utilizzo di studio e professionale quale Libre Office che è compatibile con il pacchetto Microsoft, Adobe Reader, Gimp per realizzazioni grafiche, Inkscape per la grafica 3D, Diagram Editor che è un potente programma per la schematizzazione grafica di flussi operativi, Google Chrome, Firefox ed i pacchetti di base rilasciati con l’installazione del sistema operativo Gnu/Linux Ubuntu LTS.
Per quanto riguarda i pacchetti software pre-installati sui Computer Ricondizionati, con il sistema operativo Microsoft Windows 10 Professional, verranno installati Gimp, Inkscape, Adobe Reader, Libre Office, Google Chrome, Firefox e tutti i pacchetti che la Microsoft rilascia in fase di installazione.
Il case non influirà sul prezzo stimato in quanto qualora non dovesse essere sostituito come per il case brand, con il lavoro supplementare che verrà effettuato per la sua sanificazione, per i vari collegamenti personalizzati etc, coprirà il costo del case nuovo per cicli di tempo di lavoro del nostro personale.
Eventuali upgrade hardware di memorie ed alimentatori, a seguito del fatto che la nostra azienda non intende guadagnare sull’hardware acquistato, non saranno da noi economicamente supportati, ma ribalteremo in copia, la fattura di acquisto che ci verrà inviata dal nostro fornitore con acclusa nostra fattura scaricabile contabilmente dal cliente che dovrà essere preventivamente pagata per consentirci di ottenere la merce.
Si concorderà con il cliente la modalità di acquisto e lo potremo consigliare dove poter reperire la componentistica in modo rapido e sicuro qualora intenda provvedere autonomamente.
Se il cliente per i propri Computer Ricondizionati, desiderasse il sistema operativo Microsoft Windows 10 Professional, dovrà dichiararlo via email all’atto della firma del contratto di ricondizionamento computers e dovrà comunicarci prontamente tutti i product-id necessari per l’attivazione del prodotto una volta installato il disco SSD con tale sistema operativo.
In caso di mancata dichiarazione e/o comunicazione dei product-id, nella macchina verrà montato il disco SSD con Gnu/Linux Ubuntu LTS da noi pre-configurato.
Se il cliente, per sua scelta, dovesse decidere prima della restituzione dei computers, di sostituire il sistema operativo Gnu/Linux Ubuntu LTS con il sistema operativo Microsoft, la sostituzione del disco SSD comporterà un aggravio di spesa di 25 Euro più il costo della licenza Microsoft ORIGINAL per ogni computer sul quale il nostro tecnico dovrà intervenire.
POSSO RICHIEDERE L’INSTALLAZIONE DI ALTRI SOFTWARE ?
Certamente, si può richiedere sui Computer Ricondizionati, l’installazione su sistemi Microsoft di altri software purché ne venga consegnato il supporto digitale (DVD-ROM originali) ma non verranno effettuate né personalizzazioni, né tanto meno verranno effettuate configurazioni di tali programmi e dovrà esserne provata la piena originalità con serial number rilasciati dal produttore ed il costo per ogni programma installato sarà di 12 Euro cadauno.
POSSO RICHIEDERE L’INSTALLAZIONE DI UNA STAMPANTE ?
I sistemi operativi hanno pre-installata una stampante PDF ed il problema che spesso si verifica è la mancanza dell’hardware che non ci consentirebbe di poterne testare la piena funzionalità, quindi non è possibile richiedere l’installazione di una stampante che potrete fare voi comodamente presso il vostro studio o la vostra azienda in pochissimi minuti, una volta ricollegata la macchina alla vostra postazione di lavoro.
Consigliamo vivamente di collegare la stampante al computer ed accenderla dopo il completo avvio dei sistemi operativi, per consentire a questi ultimi il perfetto riconoscimento ed evitare di utilizzare i CD di configurazione se la stampante viene riconosciuta regolarmente e dimostra piena funzionalità.
Siamo a ricordare che ogni installazione contribuisce, per i sistemi Microsoft, ad appesantirne il registry interno rallentandone spesso i processi di utilizzo e noi desideriamo che i Computer Ricondizionati lavorino sempre al massimo delle loro possibilità per soddisfare l’utilizzatore.
POSSO RICHIEDERE LA CONFIGURAZIONE DELLA SCHEDA DI RETE ?
Tutti i Computer Ricondizionati, in fase di test vengono collegati alla nostra rete interna che utilizza il DHCP standard per poter aggiornare completamente i sistemi operativi prima del test finale.
Tale configurazione è automatica per i sistemi operativi e quindi solitamente standard per chi collega il computer alla propria rete.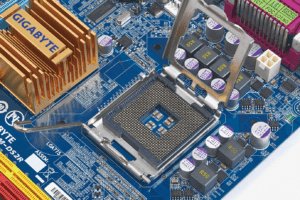
Non effettuiamo personalizzazioni delle schede di rete ma, possiamo configurarne eventuali IP, Subnet mask e Gateway secondo vostre specifiche con un costo di 5 Euro per scheda di rete (a volte ci sono computer che ne hanno più di una).
Non verrà, ovviamente, configurato alcun dominio ma verrà eventualmente su richiesta del cliente, configurato il gruppo di lavoro a cui apparterrà la macchina.
POSSO RICHIEDERE L’INSTALLAZIONE DI HARDWARE AGGIUNTIVO QUALI SCHEDE VIDEO ED ALTRO ?
I Computer Ricondizionati vengono preparati per poter funzionare al pieno delle loro massime prestazioni mai tentando overclock o altre cose che ne potrebbero compromettere sicuramente la stabilità di utilizzo nel tempo.
Qualora abbiate la necessità di installare una scheda video o una scheda di rete, questi componenti non potranno essere usati ma dovranno essere NUOVI ed accompagnati da una fattura che il rivenditore vi ha rilasciato comprensivi di tutti gli elementi hardware a corredo.
Il tempo che spesso viene speso per una ricerca guasti su un componente usato difettoso, farebbe lievitare i costi del ricondizionamento del computer e non sarebbe sicuramente soddisfacente per Voi.
L’installazione di questi eventuali componenti supplementari ha un costo di 5 Euro cadauno comprendente l’installazione di eventuali driver del produttore qualora il sistema operativo non lo riconosca autonomamente.
COME POSSO INVIARVI E RITIRARE I MIEI COMPUTERS ?
La S.H.A.D.O. GROUP srl, società nostra partner italiana, vi comunicherà dove spedire i vostri computer per il ricondizionamento operando in una sede vicino Roma (Italy).
Verrà convenuto con i tecnici della S.H.A.D.O. GROUP srl il ritiro dei vostri computer che dovranno essere consegnati ad un corriere con il quale avrete preso accordi anche perché le spese sono vostro carico.
Il giorno del ritiro dei computer, sarà indicato a mezzo email appena le macchine saranno completamente pronte e potrete così prendere accordi con il vostro corriere per data/ora.
I nostri consulenti sono a vostra completa disposizione, se siete seriamente interessati non pensateci e contattateci




 Online scams have become very profitable for phantom companies, and an asiatic State, as always, is the master, since although it can boast of very serious and reliable companies, it proves to have no control bodies to search online for its compatriots who play with the lives of companies and people by carrying out all kinds of commercial crimes, especially in the name of companies that have never had business relations with them and are completely unaware of what is happening
Online scams have become very profitable for phantom companies, and an asiatic State, as always, is the master, since although it can boast of very serious and reliable companies, it proves to have no control bodies to search online for its compatriots who play with the lives of companies and people by carrying out all kinds of commercial crimes, especially in the name of companies that have never had business relations with them and are completely unaware of what is happening
 Ecommerce in Malta, a system related to online sales that we can assure you, works perfectly without creating problems for either sellers or buyers, in spite of what many exclusively Italian and German journalistic sources try in every way to discredit because obviously, they have to pull the water to their own mill
Ecommerce in Malta, a system related to online sales that we can assure you, works perfectly without creating problems for either sellers or buyers, in spite of what many exclusively Italian and German journalistic sources try in every way to discredit because obviously, they have to pull the water to their own mill







 Avere un sito web professionale non è una cosa semplice in quanto vanno tenuti presenti molti fattori che ne determineranno il successo e soprattutto l’indice di gradevolezza per i futuri clienti
Avere un sito web professionale non è una cosa semplice in quanto vanno tenuti presenti molti fattori che ne determineranno il successo e soprattutto l’indice di gradevolezza per i futuri clienti
 Refurbished Computers for businesses and professionals, certainly allow you to save up to 60% compared to the price of a new product of equal performance
Refurbished Computers for businesses and professionals, certainly allow you to save up to 60% compared to the price of a new product of equal performance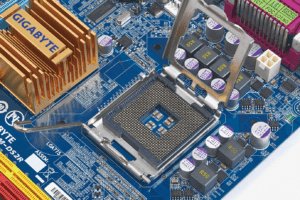


 All refurbished computers are connected to our internal network during testing, which uses standard DHCP in order to fully upgrade operating systems before the final test.
All refurbished computers are connected to our internal network during testing, which uses standard DHCP in order to fully upgrade operating systems before the final test.


 Los mini-PCs sin ventilador son geniales para este propósito ya que son pequeños, silenciosos, eficientes energéticamente y tienen de 2 a 6 puertos Ethernet en ellos soportando brillantemente el ROUTER FIREWALL OPNSENSE, y necesitarás
Los mini-PCs sin ventilador son geniales para este propósito ya que son pequeños, silenciosos, eficientes energéticamente y tienen de 2 a 6 puertos Ethernet en ellos soportando brillantemente el ROUTER FIREWALL OPNSENSE, y necesitarás
 Financing for companies thanks to SHADOIT CONSULTANCY GROUP, our partner and Maltese sister company, specialized in credit analysis
Financing for companies thanks to SHADOIT CONSULTANCY GROUP, our partner and Maltese sister company, specialized in credit analysis 
 Excellent Ethiopian diamonds, having hexagonal shape, are made with a special cut by the master jewelers, providing a perfect cut and taking care of the hexagonal design of nature and their reflection
Excellent Ethiopian diamonds, having hexagonal shape, are made with a special cut by the master jewelers, providing a perfect cut and taking care of the hexagonal design of nature and their reflection

 It has always been important to use safe haven assets such as gold, silver and especially investments in precious stones that represent a reliable guarantee outside of any world crisis
It has always been important to use safe haven assets such as gold, silver and especially investments in precious stones that represent a reliable guarantee outside of any world crisis


 Towards financial recovery, a hypothesis that in this period has involved the world’s economies, bringing most of the financial sectors to their knees, allowing us to see that the longed-for recovery expected by most financial operators and many private investors for 2021, will almost certainly arrive late and will be very asphyxiated contrary to what was hoped
Towards financial recovery, a hypothesis that in this period has involved the world’s economies, bringing most of the financial sectors to their knees, allowing us to see that the longed-for recovery expected by most financial operators and many private investors for 2021, will almost certainly arrive late and will be very asphyxiated contrary to what was hoped
 TECHNICAL ASSISTANCE ITALY is taken care of by the Italian staff of S.H.A.D.O. GROUP srl, a partner company of the holding SHADOIT CONSULTANCY GROUP and is interested in computer structures with professionalism and twenty years of experience gained by its technicians from various large companies
TECHNICAL ASSISTANCE ITALY is taken care of by the Italian staff of S.H.A.D.O. GROUP srl, a partner company of the holding SHADOIT CONSULTANCY GROUP and is interested in computer structures with professionalism and twenty years of experience gained by its technicians from various large companies





